Demystifying RPKI-Invalid Prefixes: Hidden Causes and Real Risks
In short:
- Despite the widespread adoption of Resource Public Key Infrastructure (RPKI), thousands of routes remain marked as RPKI-invalid, with no meaningful decline in the numbers.
- Two major causes for RPKI invalidity are opaque IP transit services and IP leasing.
- Two in five affected prefixes incur latency increases exceeding 100 milliseconds.
The Resource Public Key Infrastructure (RPKI) has become a cornerstone of Internet security. It helps networks verify whether a route announcement—essentially, a claim about who owns and operates a block of IP addresses—is legitimate. In doing so, it plays a key role in preventing route hijacking, a long-standing threat that can redirect traffic, disrupt services, or enable surveillance.
In our paper, “Demystifying RPKI-Invalid Prefixes: Hidden Causes and Security Risks,” we at Virginia Tech, in collaboration with CableLabs, conducted the first comprehensive study to understand why RPKI-invalid routes persist, identify their root causes, and measure their real-world impact on Internet routing.
What are RPKI-Invalid Prefixes
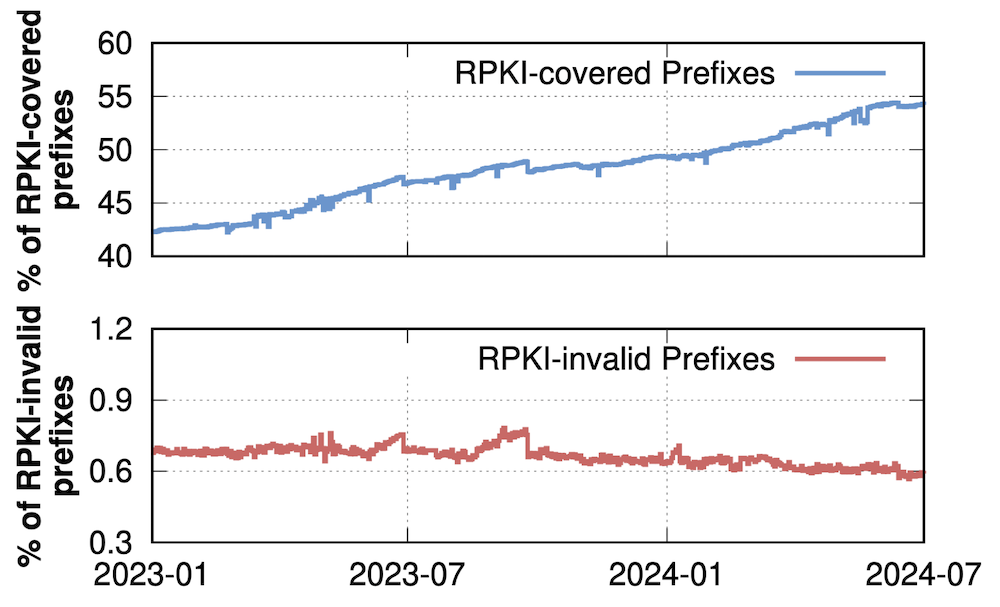
Over the past few years, RPKI adoption has grown rapidly. Today, more than half of all Internet routes are protected by cryptographic authorizations (called ROAs). This progress is widely seen as a major step forward for securing global routing.
But there is a problem. Despite widespread deployment, thousands of routes are still marked as RPKI-invalid. Our recent study finds that over 6,000 invalid routes appear in the global routing system on any given day, with tens of thousands observed over time, and that number has not meaningfully declined, as Figure 1 shows. This raises an important question: if RPKI is working, why do these invalid routes persist?
What Causes RPKI-invalid Routes?
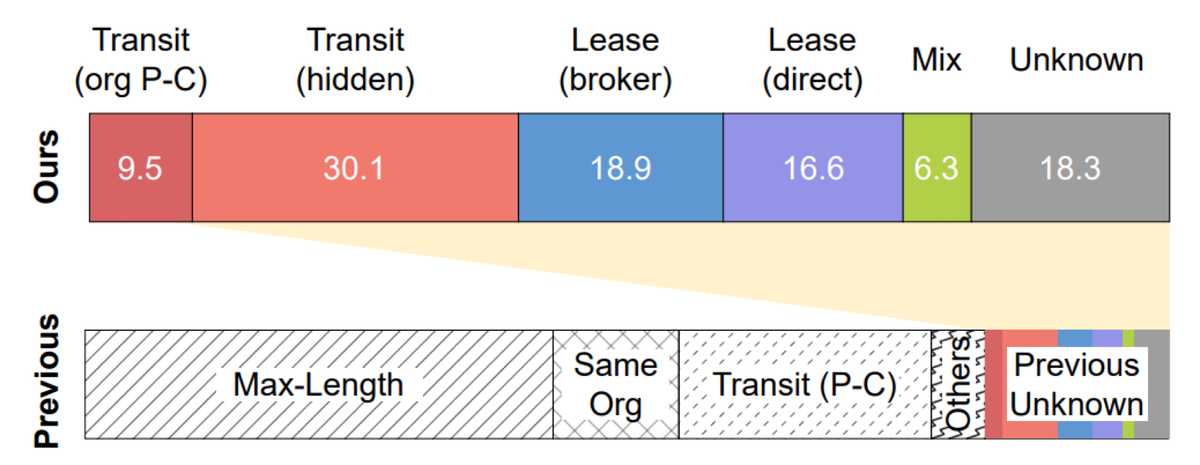
In addition to well-known and easily detectable misconfigurations, such as those between ASes under the same organizations, we identified two major, less visible root causes of RPKI invalidity:
IP Leasing
As IPv4 addresses become increasingly scarce, organizations often lease IP prefixes instead of owning them directly. In most cases, the original owner retains control of the RPKI records, while the lessee announces the prefixes in BGP.
Problems arise when the RPKI authorization is not updated to include the lessee’s network. As a result, perfectly legitimate routing announcements can be marked as invalid—not because of an attack, but due to a lack of coordination between parties.
Opaque IP Transit
Modern network services, such as DDoS mitigation or traffic tunneling, can obscure the true origin of a prefix. In these setups, a provider may announce a customer’s prefix in its own network, while forwarding traffic internally to the customer.
From the perspective of RPKI, the observed origin no longer matches the authorized one, so the route is classified as invalid. These practices are often intentional and operationally necessary, but they do not always align with current validation models.
Together, we found that more than 96% of the RPKI-invalid prefixes in today’s IPv4 routing tables collected from Routeviews are caused by misconfigurations that we can explain and classify in Figure 2.
What are the Real-world Impacts?
These RPKI-invalid routes have tangible consequences for Internet operations. To measure the real-world impact, we launched Internet Control Message Protocol (ICMP) ping and traceroute measurements from more than 5,000 RIPE Atlas probes across over 1,600 ASes worldwide, targeting active hosts within over 4,000 RPKI-invalid prefixes. We found
- 3.1% of RPKI-invalid prefixes experience connectivity loss from at least one network vantage point. This observation challenges the assumption that invalid routes are harmless as long as a fallback path is available, a common assumption today.
- 18.5% of RPKI-invalid prefixes experience unintended routing changes. These reroutes frequently bypass upstream networks intended to provide security services such as DDoS mitigation or traffic inspection. The performance impact is significant: nearly all affected prefixes experience increased latency, and 39.2% incur latency increases exceeding 100 milliseconds. Many also traverse substantially more AS hops, increasing exposure to congestion and attack surfaces.
Move Beyond Passive Hygiene
The persistence of RPKI-invalid routes underscores a critical gap between cryptographic authorization and the operational realities of modern IP transit and leasing. Bridging this gap requires the community to move beyond passive ROA creation and adopt proactive routing hygiene.
First, network operators must align their practices with initiatives like MANRS (Mutually Agreed Norms for Routing Security). Adhering to MANRS guidelines ensures that organizations not only filter invalid routes but also maintain strict coordination between their routing intent and their RPKI records.
For organizations involved in IP leasing or complex transit arrangements—such as DDoS mitigation scrubbing centers—manual ROA management is no longer viable. Operators must integrate ROA creation and deletion directly into their automated network provisioning pipelines to prevent the coordination failures that cause the vast majority of these invalids.
Furthermore, the community must shift from a "set and forget" mentality to continuous RPKI state validation. Leveraging proactive monitoring tools to alert on BGP origin mismatches before they propagate globally is essential. Discussions within the IETF SIDROPS (SIDR Operations) Working Group highlight the pressing need for such operational guidelines and improved tooling.
Ultimately, RPKI remains the bedrock of global routing security, but its efficacy depends on evolving our operational models to match the structural complexity of today's Internet. We urge network operators to audit their current IP leasing and transit configurations, and we invite researchers and policymakers to collaborate on more flexible authorization models that accommodate legitimate opaque routing practices without compromising security.
Read our paper and follow our presentation at NDSS 2026 to learn more.
Weitong Li is a postdoctoral researcher at Virginia Tech, where his work focuses on measuring and securing Internet routing infrastructure.
The views expressed by the authors of this blog post are their own and do not necessarily reflect the views of the Internet Society.

