Mapping Community Responses to Cloud Security Misconfigurations
In short:
- Human error-attributed misconfigurations are the leading cause of security and privacy incidents in cloud services.
- Researchers recently reviewed 251K security and privacy-related posts on Stack Overflow to understand what are the real-world challenges developers, system administrators, and network engineers are asking for assistance.
- Technical errors, usability failures, and insufficient support systems are the primary cause for errors.
Cloud computing has become integral to modern software development due to its scalability, affordability, and ease of deployment. However, securely configuring cloud services remains a significant challenge for developers, system administrators, and network engineers.
Misconfigurations resulting from human error remain a leading cause of security and privacy incidents, often stemming from the complexity of configuring cloud platforms. In July 2024, for example, attackers accessed call and text records of over 100 million AT&T customers by exploiting improperly secured Snowflake databases that lacked enforced multi-factor authentication.
These are not one-off incidents but rather systemic issues in the cloud ecosystem; a recent report investigating production assets across major cloud providers such as Azure, AWS, and Google Cloud found that cloud assets have an average of 115 vulnerabilities.
This landscape underscores the urgent need to understand where and how such misconfigurations persist, from a human-centric perspective.
My colleagues and I recently tackled this challenge by analyzing interactions among operators on Stack Overflow, a popular question-and-answer website for computer programmers.
This provides a unique lens into the real-world challenges of cloud security configuration and how the cloud operator community responds to them.
Challenges Stem From Technical Errors, Usability Failures, and Insufficient Support Systems
We analyzed and mapped common cloud configuration challenges from more than 251K security and privacy-related posts on Stack Overflow published between 2008 and 2024 (Figure 1).
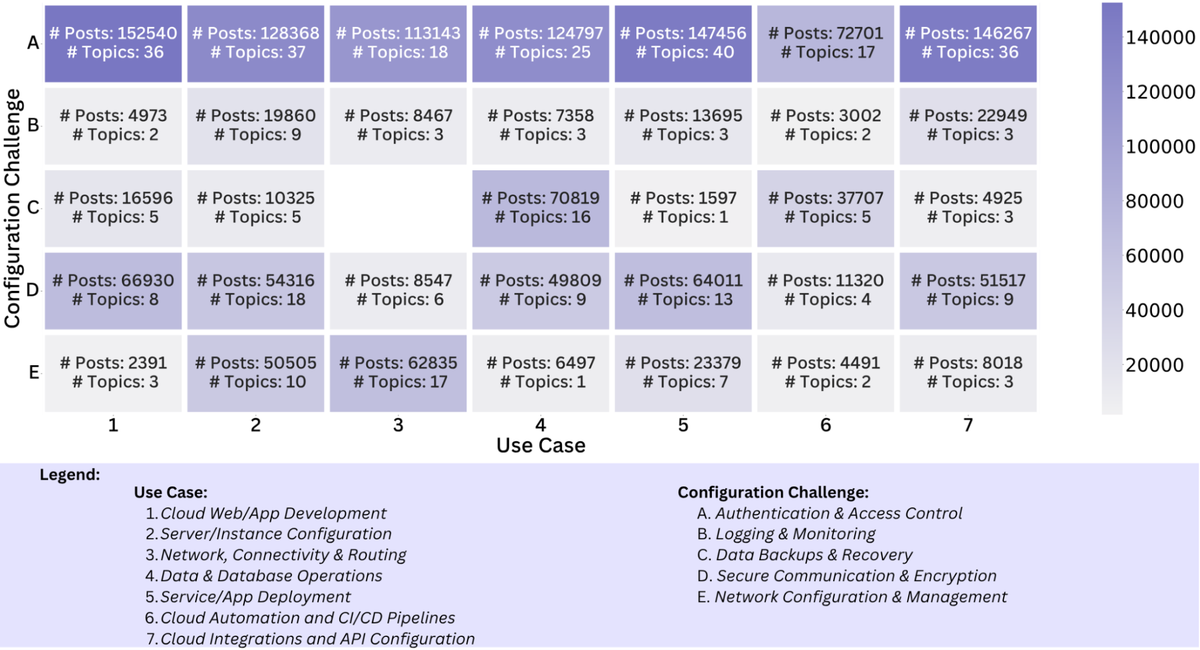
Among these, authentication and access control emerged as the most prevalent challenge, cutting across nearly all cloud use cases. Other common issues were:
- secure communication and encryption
- network configuration and management
- logging and monitoring
- database backup and recovery.
Misconfigurations in authentication and access control cascade into failures across other domains (for example, networking, deployment, and development), underscoring the need for a holistic understanding of identity and access mechanisms in secure cloud systems.
These challenges stem not only from technical errors but from broader usability failures and insufficiently tailored support systems. This includes impractical, incomplete, or overly generic documentation, as well as a lack of context-aware tools to guide developers and administrators through complex configuration tasks. Together, these issues reveal a persistent disconnect between available support resources and the practical realities of cloud development, underscoring the need for more actionable, comprehensible, and context-aware support mechanisms.
We also analyzed the accepted answers of the 251K questions we collected. These accepted answers primarily address configuration challenges through three complementary strategies:
- code changes and explanations
- service usage suggestions
- references to official documentation.
The consistent reliance on a set of trusted help resources, often mirrored in the questions themselves, highlights a shared ecosystem of knowledge that operators and answerers depend on to resolve cloud configuration problems.
Our dataset included both narrowly scoped debugging questions and broad inquiries about the feasibility of certain cloud configurations, reflecting how the cloud landscape fosters not only technical missteps but also fundamental uncertainty. The prevalence of such questions underscores that being stuck is not the exception but the norm,, and current tools are failing to meet the needs and expectations of developers and administrators.
Can LLMs Assist in the Future?
Overall, we argue that addressing the configuration challenges requires improving the design of security and privacy tools and feedback mechanisms, especially around authentication and access control, and expanding context-aware, socially and organizationally informed help resources.
Future work should investigate how fine-tuned LLMs can be integrated and deployed within operators’ cloud configurations to provide context-sensitive help when required. These LLMs would be fully aware of the capabilities and limitations of operators’ setups and, therefore, offer more contextualized advice. Future work should also focus on curating accurate training data for these LLMs to avoid training on potentially erroneous data.
Read our NDSS 2026 paper to learn more about our methodology and results.
Sumair Ijaz Hashmi is a Doctoral Researcher at the CISPA Helmholtz Center for Information Security in Germany.
The views expressed by the authors of this blog post are their own and do not necessarily reflect the views of the Internet Society.